Russian-speaking hackers knock US state government websites offline
Oct 6, 2022, 7:00 AM
Russian-speaking hackers on Wednesday claimed responsibility for knocking offline state government websites in Colorado, Kentucky and Mississippi, among other states. (Jack Guez/ via Getty Images)
(Jack Guez/ via Getty Images)
(CNN) — Russian-speaking hackers on Wednesday claimed responsibility for knocking offline state government websites in Colorado, Kentucky and Mississippi, among other states — the latest example of apparent politically motivated hacking following Russia’s invasion of Ukraine.
The Kentucky Board of Elections’ website, which posts information on how to register to vote, was also temporarily offline on Wednesday, but it was not immediately clear what caused that outage. The board of elections’ website is also managed by the Kentucky government, though the hackers did not specifically list the board as a target.
The websites in Colorado, Kentucky and Mississippi were sporadically available Wednesday morning and afternoon as administrators appeared to try to bring them online.
It’s an example of the type of digital disruption or distraction that US officials and election officials are preparing for ahead of the November midterm elections. Websites like that of the Kentucky Board of Elections are not directly involved in the casting or counting of votes, but they can provide useful information for voters.
“The [hacking] campaign does not appear to specifically target U.S. elections infrastructure, though election-related websites can be indirectly or directly impacted through the broader operation,” the Elections Infrastructure Information Sharing & Analysis Center (EI-ISAC), a nonprofit-backed threat-sharing center, said in an email to election officials obtained by CNN.
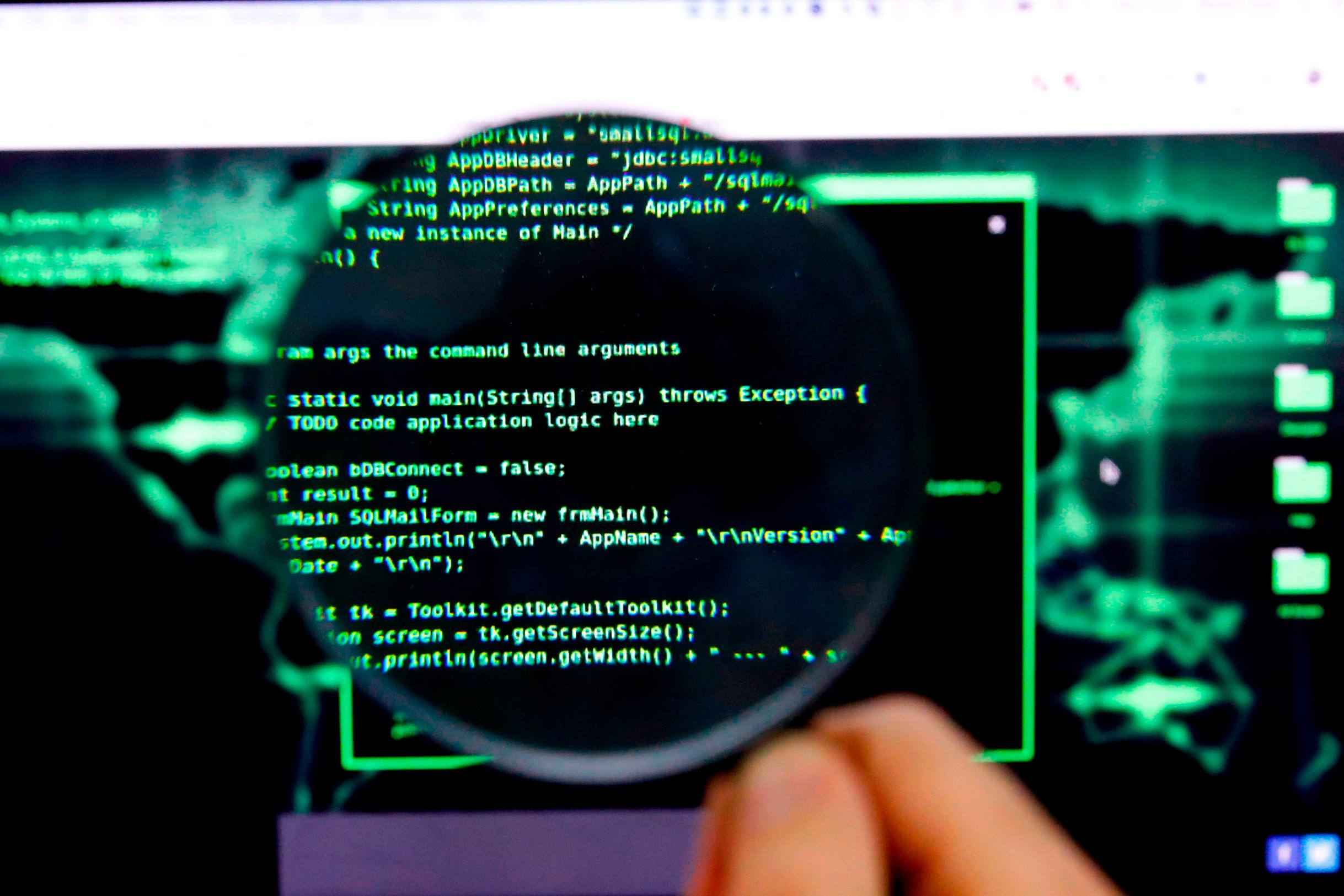
The hacking group claiming responsibility for Wednesday’s website outage is known as Killnet and stepped up their activity after Russia’s February invasion of Ukraine to target organizations in NATO countries. They are a loose band of so-called “hacktivists” — politically motivated hackers who support the Kremlin but whose ties to that government are unknown.
The group also claimed responsibility for briefly downing a US Congress website in July, and for cyberattacks on organizations in Lithuania after the Baltic country blocked the shipment of some goods to the Russian enclave of Kaliningrad in June.
Multiple states have confirmed intermittent connection issues to their websites following suspected cyberattacks, according to the notice from EI-ISAC, which works closely with the federal government on election security.
By Wednesday afternoon, the websites of Mississippi and Kentucky, including Kentucky’s Board of Elections, were back online. The Colorado state website was still struggling to load.
The Colorado governor’s Office of Information Technology said it took a state web portal offline “due to a cyberattack claimed by an anonymous suspected foreign actor.”
“All other State of Colorado websites and essential state government services are online and available,” the statement said. The state has a temporary website to provide Coloradans with information on state services, the statement said, adding that there was no timetable for the original website’s restoration.
CNN has requested comment from US Cybersecurity and Infrastructure Security Agency (CISA), which works with states on election security.
“Some Kentucky.gov state websites have been experiencing abnormal traffic, resulting in intermittent interruptions,” Carlos Luna, general manager of Kentucky Interactive, a contractor that manages Kentucky government websites, said in a statement to CNN. “We continue to investigate and are working with the commonwealth to mitigate the issue.”
A Mississippi government spokesperson did not return a request for comment by publication time.
Officials at the FBI and CISA reiterated this week that any efforts by hackers to breach election infrastructure are “unlikely to result in largescale disruptions or prevent voting.”
The hacking group listed the US state websites — which state governments use to promote tourism and offer resident services — as among their target list for cyberattacks on the Telegram social media app beneath a picture that read “F — NATO.” They typically conduct crude hacks that temporarily knock websites offline but don’t do further damage to infrastructure.
Killnet thrives off of public attention and bravado, and cybersecurity experts have to strike a balance between being mindful of Killnet’s online antics and not hyping a low-level threat.
“We do not want to build up this group or convey a false sense of doom to scare people or give Killnet unwanted publicity,” Jason Passwaters, chief operating officer of security firm Intel 471, previously told CNN. “This group is capable of causing disruptions, but it’s up to organizations to understand what kind of risk Killnet actually poses to their operations.”
This story has been updated with additional details Wednesday.